This article was originally reported on Dunia on March 24, 2026.
[Editor’s Note] On January 5th, local police and South Korean authorities raided a luxury residential area in Phnom Penh, Cambodia, arresting 26 members of a South Korean cyber scam syndicate. This operation revealed that the group had extorted approximately 26.7 billion KRW (approximately USD 18 million) from 165 South Korean victims. Mekong Independent and Dunia obtained and reported on the internal documents used by this organization for their crimes. These records meticulously detailed the victims’ personal information, asset status, mobile phone models, and even their available vacation days. Dunia contacted Seoyeon Kim (a pseudonym), a victim listed in the document, to uncover the harrowing details of her “self-confinement” nightmare.
The Voice Phishing Trap Set on Christmas Eve
The festive atmosphere on December 24, 2025, was shattered for Kim by a single phone call displaying the caller ID “112”. The caller, a middle-aged man claiming to be a court official, informed her that her bank account had been used as a burner account in a crime and that she needed to undergo an investigation.
Kim recalled, “Normally, I would have dismissed it as voice phishing, but the caller spoke Korean exceptionally well. I was drawn in and genuinely believed he was calling from the court”. Under the threat of immediate arrest if she refused to cooperate, the perpetrator directed Kim to a specific website to verify an official document, prompting her to enter personal information, including her ID number.
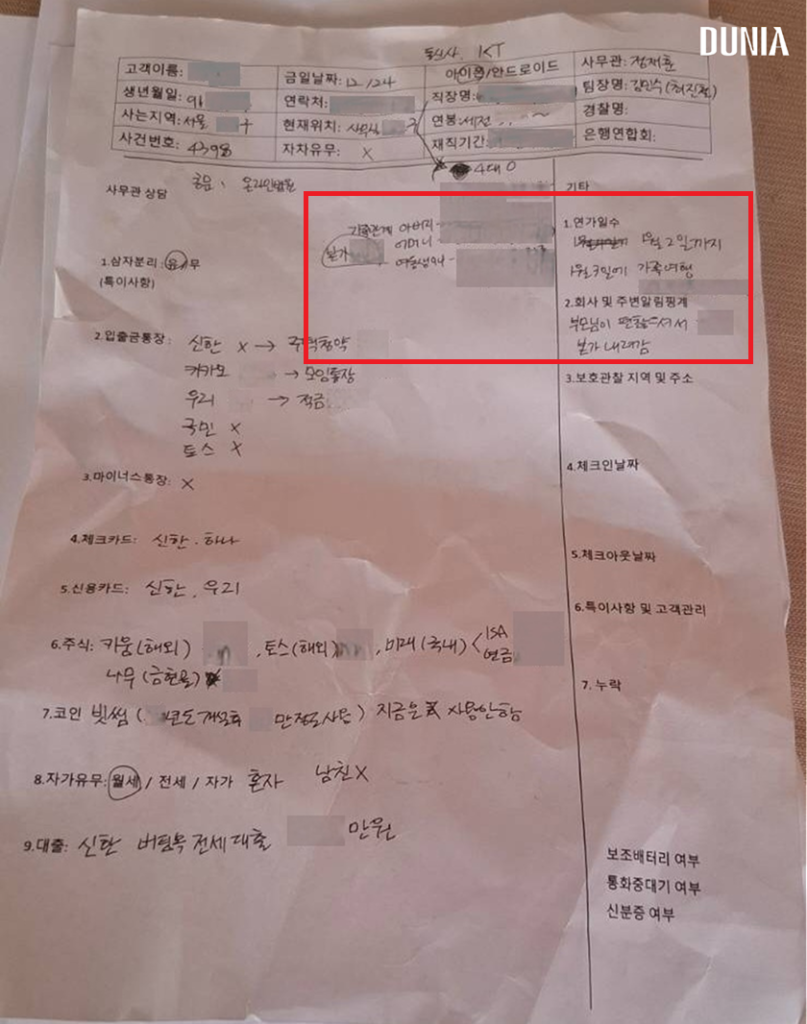
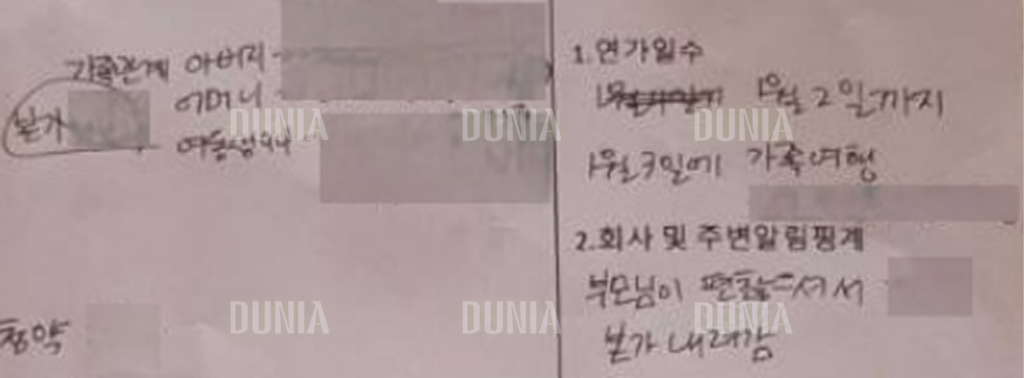
Shortly after, a man identifying himself as ‘Prosecutor Jincheol Choi’ called to extract detailed personal and financial information. The syndicate recorded these details into their own formatted documents, which were later discovered by Dunia and Mekong Independent at their Cambodian headquarters. (Related Story: Dunia Obtains Scam Files: Cambodian Ring Tracked Victims’ Every ’Annual Leave’)
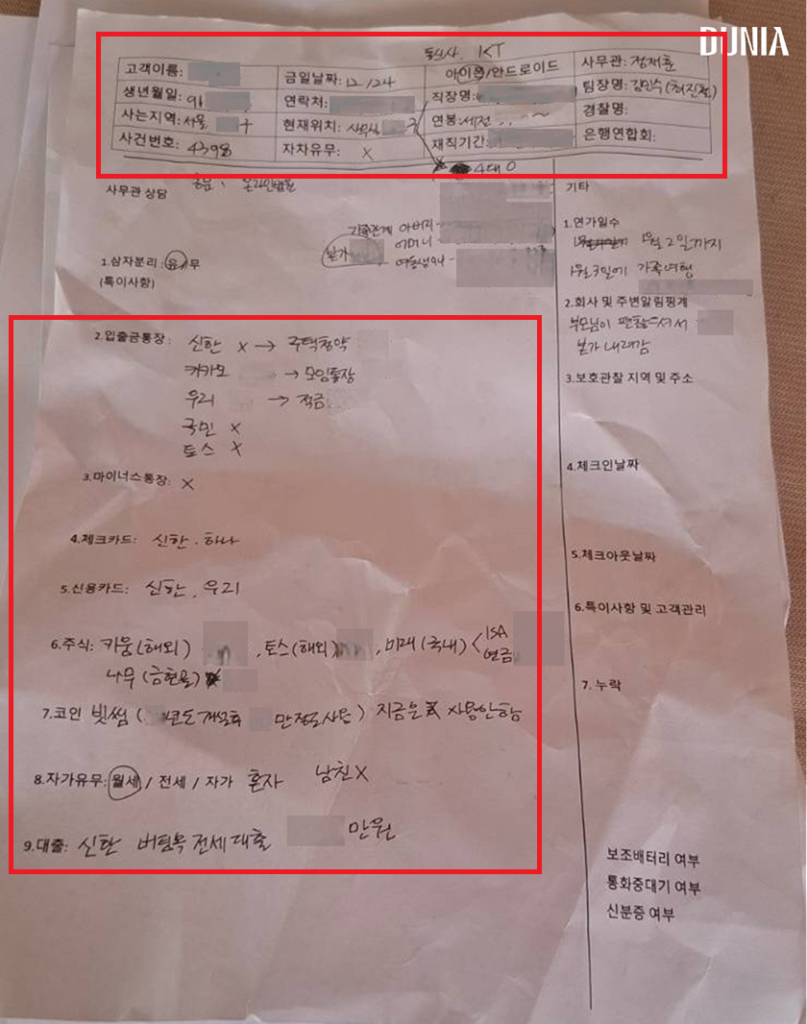
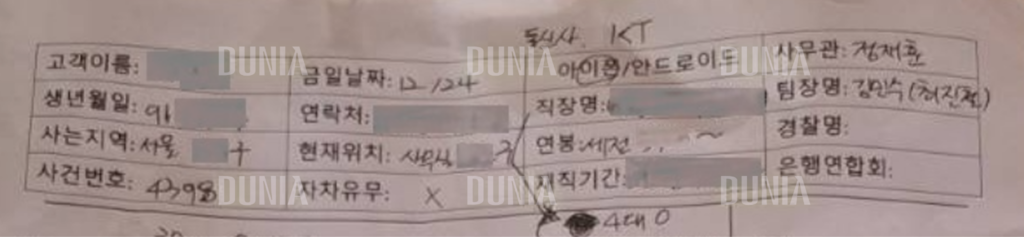
The internal document explicitly listed December 24th — the day the scammer called Kim — along with her name, date of birth, contact details, asset information, and vacation plans. The name ‘Jincheol Choi’ was also recorded under the team leader section, proving it was a fake alias used by the syndicate.
“Confined for Two Weeks”… Real-Time Reports from a Hotel Room
During a two-hour phone call where her assets were thoroughly analyzed, the impersonator pressured Kim with a stark choice: “Go to a holding cell for the investigation, or undergo a summary investigation while commuting to the agency”. Desperate to maintain her job and daily routine, Kim chose to commute.
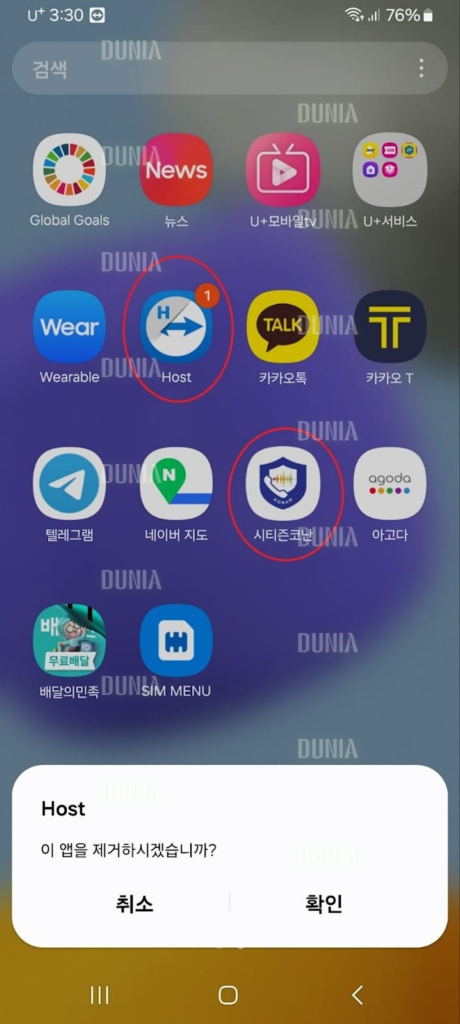
However, the syndicate immediately mandated that she be isolated from the outside world under the guise of “probation” to prevent any interference with the investigation. Their first demand was for her to replace her iPhone, claiming it could not support their required “security program”. Following their instructions, Kim purchased a used Android phone and installed a remote control application called ‘TeamViewer’.

Using this app, the scammers remotely installed a malicious program disguised as the National Police Agency’s anti-phishing app, ‘Citizen Conan’. This fraudulent app instantly hijacked the personal and financial data stored on her device upon installation. The perpetrators then instructed Kim to book and check into a hotel of her choosing for self-isolation, falsely promising that the prosecution would reimburse all expenses once the investigation concluded.

She ended up paying out-of-pocket for her accommodations and food delivery at a budget hotel in Dobong-gu, Seoul, and another hotel in Uijeongbu, which served as her “temporary probation centers”.
Strict Surveillance and Deceptive Tactics
“They told me to send a picture of the hotel room as soon as I checked in. I also suspect they tracked my location through the app they made me install,” Kim stated.
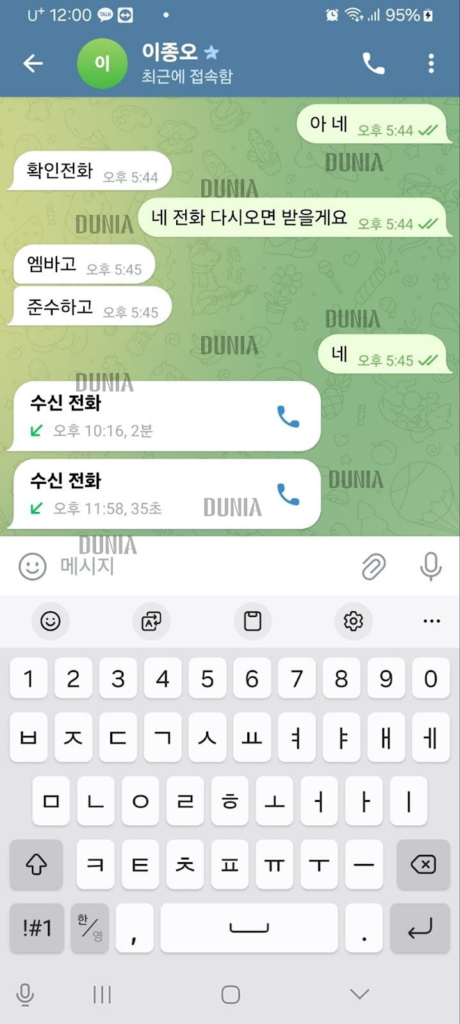
When later asked why she hadn’t reached out to family or friends, Kim explained that the scammers strictly forbade it, warning that sharing the situation would be considered an “obstruction of investigation”. They even demanded that she communicate via Telegram, imposing an ’embargo’ on her situation.
The surveillance was relentless. Once isolated, another individual claiming to be Beomjun Kwak, an official from the Financial Supervisory Service (FSS), began calling her every hour to receive status reports. The name matched a real FSS official, and the caller ID mirrored the FSS’s actual main phone number, further cementing Kim’s belief in the elaborate ruse. At their behest, she even lied to her employer, claiming she had to take time off and visit her hometown to care for sick parents — an excuse explicitly noted in the scammers’ internal documents.
“Borrow from Your Mom”… A Total of USD 182,000 Extorted
With Kim effectively trapped in “self-confinement,” the syndicate began systematically draining her assets. They convinced her to max out all available loans under her name, arguing it was necessary to prevent criminals from taking out illegal additional loans using her identity. “Under that pressure, I took out nearly 70 million KRW (approximately USD 47,100) in loans and transferred it all,” she explained.
She also sold her stocks and transferred cryptocurrency worth approximately 40 million KRW (approximately USD 27,000) in Binance Coin to their designated crypto wallets on December 30, 2025 and January 1, 2026. The extortion didn’t stop there. Claiming they had found another burner account holding 180 million KRW, they demanded a “deposit”. Exhausted of her own funds, Kim borrowed roughly 90 million KRW from her mother, with her final transfer made on January 5, 2026. In total, she lost 270 million KRW (approximately USD 182,000) to the Cambodia-based scammers.
“All transfer-related communication was done via Telegram. Once I couldn’t send any more money, they told me it was almost over and ordered me to delete Telegram and the remote control app. I still regret doing that,” she lamented.
The Police Raid, Sudden Silence, and Neglected Victims
On the afternoon of January 6, 2026, the incessant hourly phone calls and Telegram messages abruptly stopped. It was her 14th day of confinement since December 24, 2025, and notably, the day after the massive police raid and arrests of the Korean scammers in Phnom Penh.
Sensing something was wrong, Kim called back the FSS main number that had been contacting her, only to finally realize she had been the victim of a sophisticated voice phishing scam for the past two weeks. She immediately reported the crime to the police.
“The case was transferred to the Seoul Metropolitan Police Agency. I know the name of my investigator… but I haven’t received a single call from them. I have no idea how the investigation is proceeding,” Kim said.
**There are hundreds of victims like Kim, with total damages reaching 26.7 billion KRW. While authorities boast about high-profile arrests of criminal syndicates, the victims are left in the dark regarding the progress of the investigations, with little hope of recovering their stolen funds. Dunia plans to cover the plight of these neglected cyber scam victims in a follow-up report.
